Quote: Tanko
New coins are dropping every day
https://coinmarketcap.com/new/
link to original post
There are 500 different cryptocurrencies on that list and that's not all of them. But it's not a scam, it's not a commodity, it's not a collectible, it's not a Ponzi scheme, they're all legitimate currencies. What a joke. Every single one of them is just a way for some people to get rich and other people to get poorer.
Quote:Microsoft Incident Response has identified a new remote access trojan (RAT) that is capable of stealing a wide variety of information from your computer from passwords and cryptocurrency wallet information to operating system details, device identifiers, and even camera presence data.
The most sophisticated � and perhaps the most alarming � feature of this new malware is its ability to use watchdog threads to ensure self-reinstatement if removed. Basically, it can reinstall itself.
As reported by BleepingComptuer, the StilachiRAT is used to steal digital wallet data from multiple cryptocurrency wallets including Coinbase Wallet, Phantom, Trust Wallet, Metamask, OKX Wallet, Bitget Wallet and up to 20 others.
The malware also has sophisticated reconnaissance abilities and is able to steal information from an infected PC including credentials stored in your browser, clipboard data, system information, hardware identifiers, camera presence, active Remote Desktop Protocol (RDP) sessions, and running GUI-based applications.
StilachiRAT can extract credentials from Google Chrome's local state file using Windows APIs, monitor clipboard activity for password information and crypto keys and track active windows or applications. It uses the Windows service control manager (SCM) to maintain persistence and reinstalls it automatically when the malware notices its binaries are no longer active.
t the same time, StilachiRAT can monitor active RDP sessions by impersonating logged in users. It does this by capturing information from foreground windows then cloning security tokens. This allows attackers to move laterally through a victim�s network after the malware has been deployed on RDP servers that usually host admin sessions.
StilachiRAT can also evade detection and has anti-forensics features, such as the ability to clear event logs and check for signs that its running in a sandbox in order to block malware analysis attempts. If its tricked into running in a sandbox, the RAT�s API calls are encoded to slow down further analysis.
Quote: rxwineQuote:Microsoft Incident Response has identified a new remote access trojan (RAT) that is capable of stealing a wide variety of information from your computer from passwords and cryptocurrency wallet information to operating system details, device identifiers, and even camera presence data.
The most sophisticated � and perhaps the most alarming � feature of this new malware is its ability to use watchdog threads to ensure self-reinstatement if removed. Basically, it can reinstall itself.
As reported by BleepingComptuer, the StilachiRAT is used to steal digital wallet data from multiple cryptocurrency wallets including Coinbase Wallet, Phantom, Trust Wallet, Metamask, OKX Wallet, Bitget Wallet and up to 20 others.
The malware also has sophisticated reconnaissance abilities and is able to steal information from an infected PC including credentials stored in your browser, clipboard data, system information, hardware identifiers, camera presence, active Remote Desktop Protocol (RDP) sessions, and running GUI-based applications.
StilachiRAT can extract credentials from Google Chrome's local state file using Windows APIs, monitor clipboard activity for password information and crypto keys and track active windows or applications. It uses the Windows service control manager (SCM) to maintain persistence and reinstalls it automatically when the malware notices its binaries are no longer active.
t the same time, StilachiRAT can monitor active RDP sessions by impersonating logged in users. It does this by capturing information from foreground windows then cloning security tokens. This allows attackers to move laterally through a victim�s network after the malware has been deployed on RDP servers that usually host admin sessions.
StilachiRAT can also evade detection and has anti-forensics features, such as the ability to clear event logs and check for signs that its running in a sandbox in order to block malware analysis attempts. If its tricked into running in a sandbox, the RAT�s API calls are encoded to slow down further analysis.
link to original post
Microsoft? Windows? Google? Chrome?
I'm sorry, these are unfamiliar terms in my digital life. Literally nothing runs on my machines until I type "sudo" and a really long password.
Quote: AutomaticMonkey
Microsoft? Windows? Google? Chrome?
I'm sorry, these are unfamiliar terms in my digital life. Literally nothing runs on my machines until I type "sudo" and a really long password.
link to original post
What is "sudo"? I am not familiar with that.
Quote: DRichQuote: AutomaticMonkey
Microsoft? Windows? Google? Chrome?
I'm sorry, these are unfamiliar terms in my digital life. Literally nothing runs on my machines until I type "sudo" and a really long password.
link to original post
What is "sudo"? I am not familiar with that.
link to original post
sudo is like su. The difference is that sudo executes a specified command ("sudo vi /etc/passwd" maybe), where su opens a shell.
Quote: DRich
What is "sudo"? I am not familiar with that.
link to original post
It's super user do in Linux command line
Quote: DieterQuote: DRichQuote: AutomaticMonkey
Microsoft? Windows? Google? Chrome?
I'm sorry, these are unfamiliar terms in my digital life. Literally nothing runs on my machines until I type "sudo" and a really long password.
link to original post
What is "sudo"? I am not familiar with that.
link to original post
sudo is like su. The difference is that sudo executes a specified command ("sudo vi /etc/passwd" maybe), where su opens a shell.
link to original post
Thank you, I assumed it was an application he was running.
He is the third " market maker" arrested this year.
Quote: AxelWolfBitCoin just hit 111k, I do believe that's the highest it's ever been(?)
link to original post
Yes, yes it is. That's even higher than I've ever been.
Quote: AutomaticMonkeyQuote: AxelWolfBitCoin just hit 111k, I do believe that's the highest it's ever been(?)
link to original post
Yes, yes it is. That's even higher than I've ever been.
link to original post
Lightweight! 😂😂😂
Quote:A man was arrested Friday after being accused of kidnapping an Italian tourist and torturing him for weeks inside a Manhattan home in a bid to steal the alleged victim�s bitcoin, according to officials, law enforcement sources with direct knowledge of the investigation and a criminal complaint.
I assume bitcoin is more attractive for this sort of thing, because you can transfer it in a way without a weak point like an atm or bank. Traditional kidnapping and extortion still left one with some transfer point for the cash where there was greater risk. Other than that, you have to buy stuff online and then sell it,
Quote: rxwineQuote:A man was arrested Friday after being accused of kidnapping an Italian tourist and torturing him for weeks inside a Manhattan home in a bid to steal the alleged victim�s bitcoin, according to officials, law enforcement sources with direct knowledge of the investigation and a criminal complaint.
I assume bitcoin is more attractive for this sort of thing, because you can transfer it in a way without a weak point like an atm or bank. Traditional kidnapping and extortion still left one with some transfer point for the cash where there was greater risk. Other than that, you have to buy stuff online and then sell it,
link to original post
Bitcoin is so easily traceable today by enforcement so I wouldn't use it for criminal activity.
But I think everyone involved in this knew the limitations of Bitcoin and the torturer supposedly has a bag of 1000 BTC. So I would assume he knows how it can be traced and also knows how to use it to avoid being traced.
It's rumored that there was an existing sadomasochistic relationship between these people as well as drugs which would explain how experienced crypto traders would get into a position where this would happen to begin with.
Quote:Taiwan-based cryptocurrency exchange BitoPro has confirmed a security breach resulting in the alleged theft of $11.5 million in digital assets.
The revelation came shortly after on-chain investigator ZachXBT flagged unusual wallet activity on Monday, June 2, raising questions about why the exchange did not alert users sooner.
Why are exchanges still being hacked? If you're supposed to be protecting significant assets, seems like you'd have several layers of security. And could easily afford it.
Quote: rxwineQuote:Taiwan-based cryptocurrency exchange BitoPro has confirmed a security breach resulting in the alleged theft of $11.5 million in digital assets.
The revelation came shortly after on-chain investigator ZachXBT flagged unusual wallet activity on Monday, June 2, raising questions about why the exchange did not alert users sooner.
Why are exchanges still being hacked? If you're supposed to be protecting significant assets, seems like you'd have several layers of security. And could easily afford it.
link to original post
They're not being hacked. All the major exchange thefts have been inside jobs, as far as I know.
Quote: rxwineQuote:Taiwan-based cryptocurrency exchange BitoPro has confirmed a security breach resulting in the alleged theft of $11.5 million in digital assets.
The revelation came shortly after on-chain investigator ZachXBT flagged unusual wallet activity on Monday, June 2, raising questions about why the exchange did not alert users sooner.
Why are exchanges still being hacked? If you're supposed to be protecting significant assets, seems like you'd have several layers of security. And could easily afford it.
link to original post
Just about any company or piece of software can be hacked if people invest enough time and ingenuity.
Quote: DRichQuote: rxwineQuote:Taiwan-based cryptocurrency exchange BitoPro has confirmed a security breach resulting in the alleged theft of $11.5 million in digital assets.
The revelation came shortly after on-chain investigator ZachXBT flagged unusual wallet activity on Monday, June 2, raising questions about why the exchange did not alert users sooner.
Why are exchanges still being hacked? If you're supposed to be protecting significant assets, seems like you'd have several layers of security. And could easily afford it.
link to original post
Just about any company or piece of software can be hacked if people invest enough time and ingenuity.
link to original post
I have yet to wake up and find my entire bank account gone. Perhaps no one is trying hard enough.
Quote: rxwineQuote: DRichQuote: rxwineQuote:Taiwan-based cryptocurrency exchange BitoPro has confirmed a security breach resulting in the alleged theft of $11.5 million in digital assets.
The revelation came shortly after on-chain investigator ZachXBT flagged unusual wallet activity on Monday, June 2, raising questions about why the exchange did not alert users sooner.
Why are exchanges still being hacked? If you're supposed to be protecting significant assets, seems like you'd have several layers of security. And could easily afford it.
link to original post
Just about any company or piece of software can be hacked if people invest enough time and ingenuity.
link to original post
I have yet to wake up and find my entire bank account gone. Perhaps no one is trying hard enough.
link to original post
I know that my bank account wouldn't justify someone spending more than a few hours to break into.
Quote: vegasBitcoin hit another all time high of almost 112,000 dollars. That is an increase of 39% in just the last three months. Those who think it is just a pyramid scheme have been missing out on a great opportunity. Bitcoin is here to stay. Yes it will go down and have some huge drops but it will also keep going up to new highs.
link to original post
I�m pretty confident it�s a Ponzi scheme. I�m selling all of mine next month.
Who is the ponzi master? Who promised you returns? It's a network you can join.
$
1
2
2
,
4
0
2
.
1
0
Quote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
Quote: rxwineQuote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
link to original post
What you are describing is not a Ponzi scheme unless you believe all stocks on the market that don't pay dividends are a Ponzi.
Quote: DRichQuote: rxwineQuote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
link to original post
What you are describing is not a Ponzi scheme unless you believe all stocks on the market that don't pay dividends are a Ponzi.
link to original post
No, I would just ask you to explain why stocks that don't pay dividends are legal then, and Ponzi schemes aren't?
^Bolded emphasis added.Quote: DRichQuote: rxwineQuote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
link to original post
What you are describing is not a Ponzi scheme unless you believe all stocks on the market that don't pay dividends are a Ponzi.
link to original post
This is utter nonsense; someone is profoundly confused as to the most basic facts of what a share of a joint stock enterprise (and its assets & recievables) is, in well settled law (for centuries) and implemented every day in routine actual practice when assets of companies are liquidated and distributed as defined in mandatory priority of claimants. It is really not a good idea for someone to be doing any kind of self-directed investing for their own account without that most basic fundamental understanding, and it would be even more unwise to think of getting anywhere near owning any bonds and similar financial assets, public or private, on your own without financially literate supervision, if someone feels they don't want to be bothered to know what they actually legally own when purchasing these financial instruments, beyond "number go up; number go down."
I own some bitcoin - not a great deal - if it crashes I won't shed too many tears
I have profited and hope to continue to profit due to my belief that there very well may be Greater Fool than I willing to pay a higher price for it_______________(-:}
AI Overview:
Bitcoin is often cited as an example of the "greater fool theory". This theory suggests that the value of an asset is not based on its intrinsic worth, but rather on the willingness of someone else to pay a higher price for it later. In the case of Bitcoin, critics argue that it lacks intrinsic value and is primarily driven by speculation and the expectation that someone else will buy it at a higher price in the future.
.
Quote: DrawingDead^Bolded emphasis added.Quote: DRichQuote: rxwineQuote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
link to original post
What you are describing is not a Ponzi scheme unless you believe all stocks on the market that don't pay dividends are a Ponzi.
link to original post
This is utter nonsense; someone is profoundly confused as to the most basic facts of what a share of a joint stock enterprise (and its assets & recievables) is, in well settled law (for centuries) and implemented every day in routine actual practice when assets of companies are liquidated and distributed as defined in mandatory priority of claimants. It is really not a good idea for someone to be doing any kind of self-directed investing for one's own account without that most basic fundamental understanding.
link to original post
Shares of stock and Ponzi schemes are very different animals, but both of them have a few things in common. Both a Ponzi scheme and stocks will collapse unless investors are willing to invest new money.
Bernie Madoff ran a Ponzi scheme that relied on new investors. It was illegal; he went to jail, and the government recovered most of the investors' money.
Computer Associates cooked their books for years, presenting a very rosy picture to investors while it was bleeding from a thousand tiny cuts. It was illegal; people went to jail, the government collected hundreds of millions in fines, but I don't believe anything was done for the investors.
Companies with common stock are expected to adhere to well-defined accounting principles and ethical obligations. Ponzi schemes are often fly-by-night operations with a veneer of respectability. They almost always offer unusually high returns to overcome investors' hesitancy.
Bitcoin is not at all analogous to shares of joint stock entities. And whether any dividends are being paid is completely irrelevant to the underlying nature what is "owned." Whether those happen to be shares in a real enterprise with actual tangible assets that ultimately enttitles one to a piece of Chevron's oil wells for example, or to a tenth of your family's farm & ranchland & cattle & timber, or is instead a share of a silly vehicle for something that's nothing but a ludicrously obvious hyper-impulsive chump-fleecing stock Cyto-scam that exists only to be shamelessly looted.
If trying to somehow find a way to somehow stretch crypto purely virtual-vehicles such as Bitcoin, that have no possible claim that could be asserted on any kind underlying asset or to any ultimate public or private guarantor, to a comparison with some kind of existing type of real-world financial entity, it seems to many that the closest comparison might be to some speculative commodity trading vehicles. But without any defined option date and without the existence of any underlying commodity. And in fact there's been a lot of discussion over the last several years of whether the CFTC (Commodity Futures Trading Commission) might or should assert jurisdiction over it. Though that's probably been made a dead issue now.
This is where the value of all national currencies comes from, and why some national currencies have more value than others. A currency from a Third World place where you can't pay the locals to do much besides kill each other and foul the streets, because that's all they know how to do, is not the same as the currency you would use to pay an American or Japanese or European worker.
Quote: rxwineQuote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
You don't make money unless more people buy in. Reason to buy in is more people later will buy in.
link to original post
You guys are pretty lost.
https://allenfarrington.medium.com/wittgensteins-money-7cac8d0635cf
Quote: DrawingDeadNo. Underlying real assets ultimately matter, and it will apparently surprise you to hear that MOST enterprises that are structured through a joint stock ownership structure do not involve any expectation of anyone "willing to invest new money" at all. And shares of entities that are liquidated often do recieve payment from a distribution of assets, or sometimes may take direct ownership of some of the actual physical assets, such as land, buildings, and equipment. It is an ownership structure, and does not necessarily need to involve anyone engaged in any trading of any of the shares to do well, or not, for its owners/shareholders.
Bitcoin is not at all analogous to shares of joint stock entities. And whether any dividends are being paid is completely irrelevant to the underlying nature what is "owned." Whether those happen to be shares in a real enterprise with actual tangible assets that ultimately enttitles one to a piece of Chevron's oil wells for example, or to a tenth of your family's farm & ranchland & cattle & timber, or is instead a share of a silly vehicle for something that's nothing but a ludicrously obvious hyper-impulsive chump-fleecing stock Cyto-scam that exists only to be shamelessly looted.
If trying to somehow find a way to somehow stretch crypto purely virtual-vehicles such as Bitcoin, that have no possible claim that could be asserted on any kind underlying asset or to any ultimate public or private guarantor, to a comparison with some kind of existing type of real-world financial entity, it seems to many that the closest comparison might be to some speculative commodity trading vehicles. But without any defined option date and without the existence of any underlying commodity. And in fact there's been a lot of discussion over the last several years of whether the CFTC (Commodity Futures Trading Commission) might or should assert jurisdiction over it. Though that's probably been made a dead issue now.
link to original post
There's no need for an underlying claim BECAUSE YOU CAN TRUST THE ISSUER.
In fiat you can't trust the issuer so you desire A BACKING.
Backing is only a requirement when there is no trust in issuance.
That's all crypto is. A worthless rock with an uncopiable signature, that I declare valuable and try to get someone to pay more for.
(I'm getting to some useful point, but don't know what it is. LOL, )

A better analogy for crypto might be Beanie Babies. Or their contemporary successor, Labubu.
Quote: rxwineI can take a metamorphic rock (magnified) and declare it valuable. It has a unique signature that can't be exactly duplicated. If you have this rock you can show that it matches its unique signature. All someone else can do is show the picture of the signature, but their rock won't match. So this rock signature is security.
That's all crypto is. A worthless rock with an uncopiable signature, that I declare valuable and try to get someone to pay more for.
(I'm getting to some useful point, but don't know what it is. LOL, )
link to original post
You pretty much just described diamonds but yeah no value there.
Bitcoins actually have to be "mined". You actually don't get to just pick up a rock.
Evaluation of Bitcoin shouldn't come without that aspect of it.
https://www.forbes.com/sites/digital-assets/2024/12/05/what-math-problems-do-bitcoin-miners-really-solve/
Quote: darkoz
You pretty much just described diamonds but yeah no value there.
Bitcoins actually have to be "mined". You actually don't get to just pick up a rock.
Evaluation of Bitcoin shouldn't come without that aspect of it.
https://www.forbes.com/sites/digital-assets/2024/12/05/what-math-problems-do-bitcoin-miners-really-solve/
link to original post
Apparently, it's not far from picking up a rock.
Quote:Creating a token on an existing blockchain: This is the easiest and most common way to create a new cryptocurrency, according to Investopedia.
Low technical barrier: It can be done with minimal to no coding skills, especially using readily available online tools and platforms like Ethereum or Binance Smart Chain.
It's turning the rock into value that's the problem.
Quote: MichaelBluejayAnything has value if someone else is willing to pay for it. There's nothing behind crypto, so it might not have *intrinsic* value, but you can sell it, because others are willing to buy it, so you can't say it has no value at all.
A better analogy for crypto might be Beanie Babies. Or their contemporary successor, Labubu.
link to original post
Yes, the federal reserve is allowing banks to hold beanie babies. You nailed it.
https://www.federalreserve.gov/newsevents/pressreleases/bcreg20250714a.htm
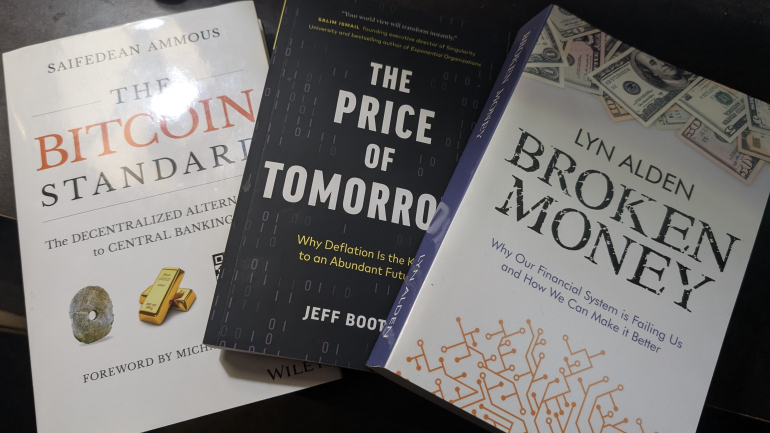
These 3 are pretty good for understanding why Bitcoin is the best money and will replace the monetary system.
how is the price of bitcoin and how are any changes in the price determined__________?
and who if anybody makes that determination________?
.
Quote: lilredrooster.
how is the price of bitcoin and how are any changes in the price determined__________?
and who if anybody makes that determination________?
.
link to original post
Just like stocks it is supply and demand. If you have more buyers than sellers it pushes the price up. People often sell to take some profit and then rebuy on dips.
Quote: vegasQuote: lilredrooster.
how is the price of bitcoin and how are any changes in the price determined__________?
and who if anybody makes that determination________?
.
link to original post
Just like stocks it is supply and demand. If you have more buyers than sellers it pushes the price up. People often sell to take some profit and then rebuy on dips.
link to original post
okay
but let's say today you have $900 million more in buys than sells
how is it determined how much the price will go up _____________?
what is the calculation_________?
.
Quote: BTLWI"A Ponzi scheme (/ˈpɒnzi/, Italian: [ˈpontsi]) is a form of fraud that lures investors and pays profits to earlier investors with funds from more recent investors.[1] Named after Italian confidence artist Charles Ponzi, this type of scheme misleads investors by either falsely suggesting that profits are derived from legitimate business activities (whereas the business activities are non-existent), or by exaggerating the extent and profitability of the legitimate business activities, leveraging new investments to fabricate or supplement these profits"
Who is the ponzi master? Who promised you returns? It's a network you can join.
link to original post
"Bitcoin resembles a penny-stock pump-and-dump scheme more than a Ponzi scheme. In a pump-and-dump scheme, traders acquire basically worthless stock, talk it up and perhaps trade it among themselves at rising prices before unloading it on to those drawn in by the chatter and the price action. Like the pump-and-dump scheme, bitcoin taps into the pure desire for capital gains...an economic analysis of bitcoin must recognise its uniqueness in the history of manias. As an object of speculation, bitcoin is unprecedented in the degree to which there is no there there...In a crash, the holders of bitcoin will collectively have lost what they have paid the miners for their bitcoin. Bitcoin holders will have no one to pursue to recover this sum: it will simply have gone up in smoke, a social loss."
Quote: lilredroosterQuote: vegasQuote: lilredrooster.
how is the price of bitcoin and how are any changes in the price determined__________?
and who if anybody makes that determination________?
.
link to original post
Just like stocks it is supply and demand. If you have more buyers than sellers it pushes the price up. People often sell to take some profit and then rebuy on dips.
link to original post
okay
but let's say today you have $900 million more in buys than sells
how is it determined how much the price will go up _____________?
what is the calculation_________?
.
link to original post
I believe you have to take the total market cap of the crypto divide it by the dollar amount of sells or buys and whatever is greater determines the up or down price. Bitcoin is over 2 trillion market cap. It gets complicated because they also add in other factors like slippage. Don't quote me on this but it is how I think it works.
Quote: BTLWI
There's no need for an underlying claim BECAUSE YOU CAN TRUST THE ISSUER.
In fiat you can't trust the issuer so you desire A BACKING.
Backing is only a requirement when there is no trust in issuance.
link to original post
Every Fiat currency has failed over time so my assumption is that trend will continue, including the U.S. dollar.
Quote: DRichQuote: BTLWI
There's no need for an underlying claim BECAUSE YOU CAN TRUST THE ISSUER.
In fiat you can't trust the issuer so you desire A BACKING.
Backing is only a requirement when there is no trust in issuance.
link to original post
Every Fiat currency has failed over time so my assumption is that trend will continue, including the U.S. dollar.
link to original post
Which non-Fiat currency has succeeded over time? As no nation's currency is a no-fiat one, I'd argue that every non-fiat-based currency failed and evolved into the fiat system the world has used for at least the last fifty years.
We will all die, and the USofA will be subjected to history books someday, but it won't be because the dollar wasn't backed by silver.
It might be because of the population's addiction to plastic.
Edited as non-fiat and fiat was reversed in one sentence.